Critical Linux Kernel Vulnerability Disclosed Affecting Major Distributions
Here's what it means for you.
If you rely on Linux systems, especially in multi-tenant environments, you need to prioritize patching to avoid potential security breaches.
Why it matters
This vulnerability affects virtually all major Linux distributions, posing significant risks to organizations using shared environments.
What happened (in 30 seconds)
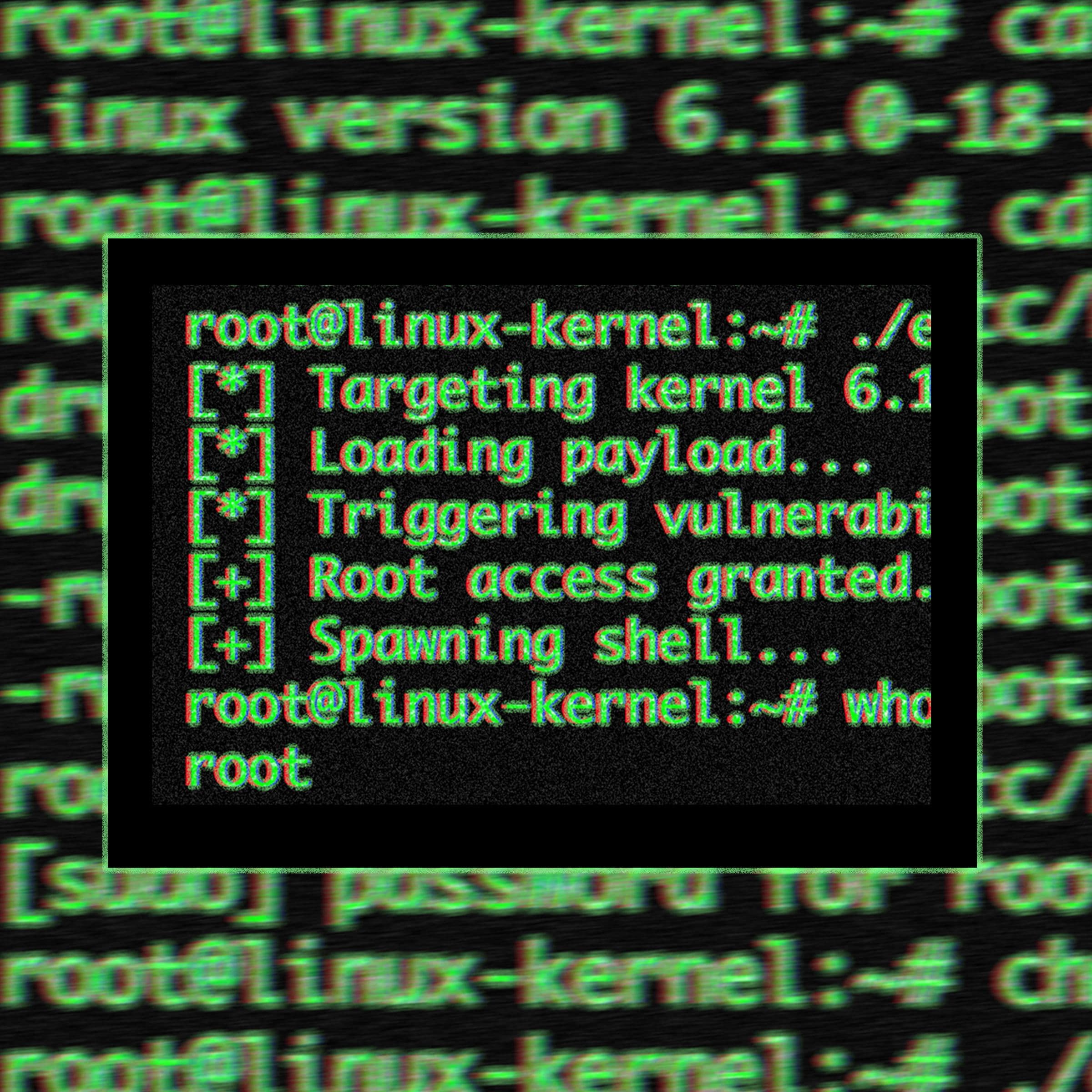
- CopyFail (CVE-2026-31431) was publicly disclosed on April 29, 2026, allowing unprivileged users to gain root access.
- The flaw stems from a logic error in the Linux kernel's crypto API, impacting distributions like Ubuntu, Red Hat, and Debian since 2017.
- Patches were committed on April 1, 2026, with major distributions rolling out updates shortly after the public disclosure.
The context you actually need
- The vulnerability was discovered by researchers at Theori using AI-assisted scanning, highlighting the growing role of AI in cybersecurity.
- It parallels previous kernel vulnerabilities like Dirty Pipe and Dirty Cow, but allows for deterministic exploitation without race conditions.
- The rapid response from major distributions indicates a heightened awareness of security risks in the open-source community.
What's really happening
CopyFail (CVE-2026-31431) is a local privilege escalation vulnerability that has raised alarms across the tech industry due to its potential impact on Linux systems. Discovered by Taeyang Lee from Theori, the flaw allows unprivileged local users to exploit a logic error in the Linux kernel's crypto API. This vulnerability is particularly concerning because it affects virtually all major Linux distributions released since 2017, including widely used systems like Ubuntu, Red Hat Enterprise Linux, SUSE, Debian, and Amazon Linux.
The root of the issue lies in a 2017 commit that optimized authenticated encryption operations in the AF_ALG socket interface. This optimization inadvertently introduced a flaw in the authencesn cryptographic template, allowing attackers to overwrite the page cache of any readable file without triggering writeback. The exploit is executed through a concise 732-byte Python script, making it accessible for attackers to gain root access with minimal effort.
The implications of this vulnerability are profound, especially in multi-tenant environments such as Kubernetes clusters and CI/CD pipelines, where shared kernel resources increase the risk of exploitation. Organizations that rely on Linux servers for cloud computing, telecommunications, and government systems are particularly vulnerable, as they often operate in environments where multiple users share the same kernel.
The response from the Linux community has been swift, with patches committed to upstream kernels on April 1, 2026, and major distributions issuing updates shortly after the public disclosure. However, the timing of the disclosure has drawn criticism, as it created a zero-day patch gap, leaving systems exposed before patches were widely available. The Cybersecurity and Infrastructure Security Agency (CISA) has since added CopyFail to its Known Exploited Vulnerabilities catalog, mandating federal remediation by specific deadlines.
Despite the rapid deployment of patches, experts have emphasized the importance of immediate action from organizations to reboot systems post-update to mitigate risks. The community's focus on multi-tenant setups highlights the need for enhanced security measures in shared environments, as the potential for exploitation remains high.
Who feels it first (and how)
- IT Security Teams: Responsible for patch management and vulnerability assessments.
- DevOps Engineers: Working in multi-tenant environments like Kubernetes clusters face immediate risks.
- Cloud Service Providers: Entities relying on Linux servers for cloud computing services must prioritize updates.
- Government Agencies: Organizations using Linux for critical infrastructure need to ensure compliance with CISA mandates.
What to watch next
- Patch Adoption Rates: Monitor how quickly organizations implement the patches to gauge overall security posture.
- Incident Reports: Watch for any reports of exploitation attempts or breaches related to CopyFail.
- Community Response: Observe discussions in the open-source community regarding best practices for securing multi-tenant environments.
The vulnerability affects major Linux distributions and has been publicly disclosed.
Organizations will face increased scrutiny regarding their patch management practices.
The extent of potential exploitation in the wild remains uncertain.
This article was generated by AI from 6 verified sources and reviewed by A47 editorial systems.
Emerging technologies, digital transformation, IT, and cultural impact of tech.
"WIRED covers the intersection of technology, culture, and politics with a progressive, forward-looking editorial stance."
— A47 Editor
Dangerous New Linux Exploit Gives Attackers Root Access to Countless Computers
A critical security vulnerability known as 'CopyFail', tracked as CVE-2026-31431, has been identified in Linux systems, allowing attackers to gain root access to numerous computers and data center servers. This flaw affects nearly all Linux distribut...
Tech news, hardware, and AI tools coverage.
"PC/tech site increasingly covering AI hardware and apps."
— A47 Editor
"Copy Fail" is a rare Linux bug that can turn an unprivileged user into a root admin in seconds
A critical vulnerability known as 'Copy Fail' has been identified in Linux systems, allowing unprivileged users to escalate their privileges to root admin status in seconds. This flaw, tracked as CVE-2026-31431, was discovered by researchers at Theor...
Tech news, reviews, and analysis of consumer electronics, science, art, and culture.
"The Verge is a technology-focused media outlet known for in-depth reporting, product reviews, and coverage of the intersection between technology and culture."
— A47 Editor
Severe Linux Copy Fail security flaw uncovered using AI scanning help
A severe security flaw known as 'Copy Fail' has been discovered, affecting nearly all Linux distributions released since 2017. This vulnerability, identified as CVE-2026-31431, allows any user to gain administrator privileges through a simple Python ...
Consumer tech and culture with frequent AI coverage.
"Influential tech outlet covering AI products and policy."
— A47 Editor
Severe Linux Copy Fail security flaw uncovered using AI scanning help
A severe security flaw known as 'Copy Fail' has been discovered, affecting nearly all Linux distributions released since 2017. This vulnerability, identified as CVE-2026-31431, allows any user to gain administrator privileges through a simple Python ...
Consumer tech news, reviews, and buying guides for gadgets and electronics.
"TechRadar is known for comprehensive buying advice, hardware reviews, and consumer tech news targeted at mainstream audiences."
— A47 Editor
'An hour of scan time is all it took': "Copy Fail" flaw impacts all Linux kernels released since 2017, so patch now or face the consequences
A critical security flaw known as 'Copy Fail' has been identified, affecting all Linux kernels released since 2017. This vulnerability poses significant risks, prompting experts to urge Linux users to update their systems immediately to avoid potenti...
Curated tech headlines including AI stories.
"Influential aggregator surfacing the day’s top tech/AI links."
— A47 Editor
Researchers detail CopyFail, a now-patched Linux vulnerability that lets unprivileged users gain admin access, as many distributions have yet to add fixes (Dan Goodin/Ars Technica)
Researchers have identified a critical Linux vulnerability known as CopyFail, which allows unprivileged users to gain administrative access. Despite a patch being released, many Linux distributions have yet to implement the necessary fixes, leaving s...
In-depth coverage of hardware, software, science, and policy.
"Ars Technica provides expert technology news, hardware reviews, and analysis for a technically savvy audience."
— A47 Editor
The most severe Linux threat to surface in years catches the world flat-footed
A new and severe threat to Linux systems, named CopyFail, has emerged, impacting multi-tenant servers, CI/CD workflows, and Kubernetes containers. This vulnerability has caught the global tech community off guard, raising alarms about the security of...
In-depth reporting on tech, policy, and science including AI.
"Respected analysis for technically savvy readers, including AI topics."
— A47 Editor
The most severe Linux threat to surface in years catches the world flat-footed
A new and severe threat to Linux systems, named CopyFail, has emerged, impacting multi-tenant servers, CI/CD workflows, and Kubernetes containers. This vulnerability has caught the global tech community off guard, raising alarms about the security of...